Cybercriminals using Coronavirus pandemic conditions to distribute malware and to steal the user login credentials.
Malware Disguised as a “Coronavirus map” used by the attackers to infect the users and to take complete control of the system.
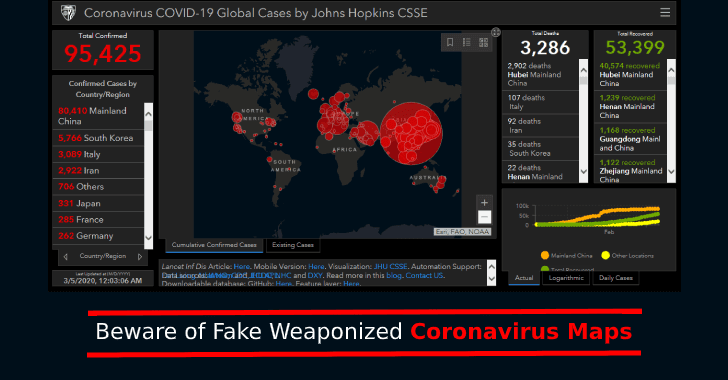
Fake Coronavirus Map
Security researchers from Reason Labs’ observed a new campaign using information stealer AZORult malware dubbed “Coronavirus map.”
The AZORult malware is known for its information stealer capabilities, it was first observed in the year 2016, the malware also acts as a downloader.
Once the malware executed on the victim’s machine it exfiltrates sensitive data. The malware generated a unique ID for every system it infected.
It steals the following credentials such as user names, passwords, credit card numbers, history, cookies and other sensitive information stored in the browser.
As the Coronavirus spreading rapidly attackers starting using its popularity to infect victims.
Once the malware installed on the system it gives a GUI interface that makes everyone believe it is an original map. Opening the malware it shows a GUI window that loads the information from the web.
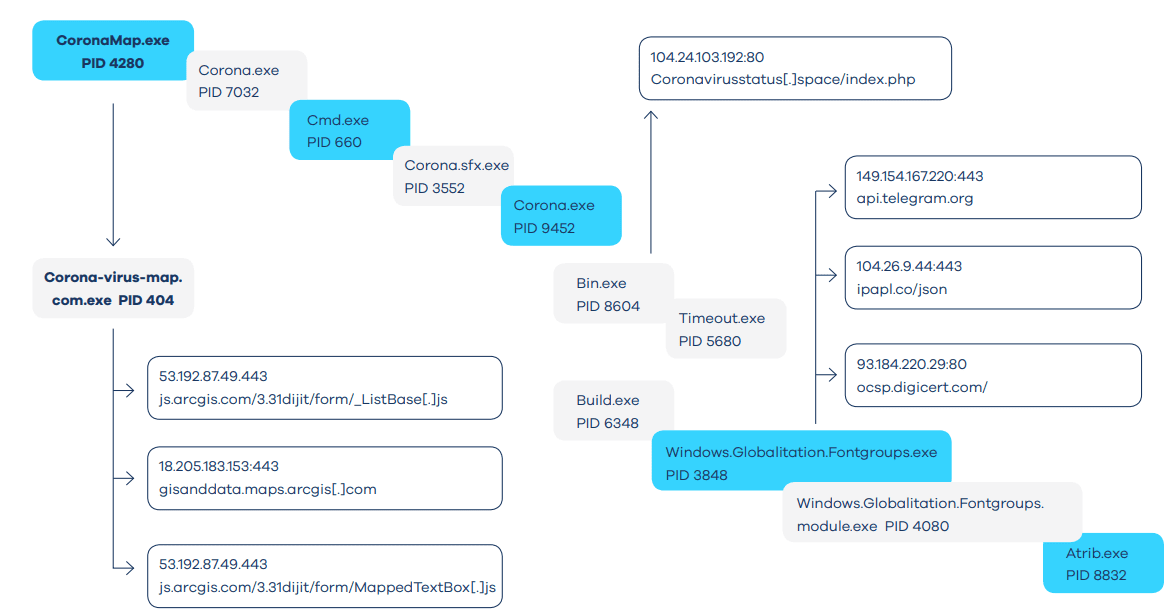
“The malware uses a few layers of packing as well as a multi-sub-process technique to make research more difficult,” reads the blog post.
The malware conducts password-stealing operation from the installed browser and creates a list called “PasswordList.txt” which stores all password information.
It is capable of stealing information from all browsers, Email clients and Cryptocurrency wallets. The following are the information shared with the C2 server.
- Basic victim’s computer information.
- Password information
- Domain name lists
- Auto-complete, cookies, and browsing history of web browser
- C2 command result
- Infected host IP address information
- Screenshots of the victim host
- Detailed system information
Users are recommended not to click on the executable files and be aware of the attachments received.
Long time supporter, and thought I’d drop a comment.
Your wordpress site is very sleek – hope you don’t mind me asking what theme you’re using?
(and don’t mind if I steal it? :P)
I just launched my site –also built in wordpress like yours– but the theme slows (!) the site down quite a bit.
In case you have a minute, you can find it
by searching for “royal cbd” on Google (would appreciate any feedback) – it’s still
in the works.
Keep up the good work– and hope you all take care of yourself during
the coronavirus scare!
No problem the theme name is Hoot Business 🙂
Thank you for comment.
What is the PHP version you running ?