Last November introduced Microsoft Azure Firewall Manager preview for Azure Firewall policy and route management in secured virtual hubs. This also included integration with key Security as a Service partners, Zscaler, iboss, and soon Check Point. These partners support branch to internet and virtual network to internet scenarios.
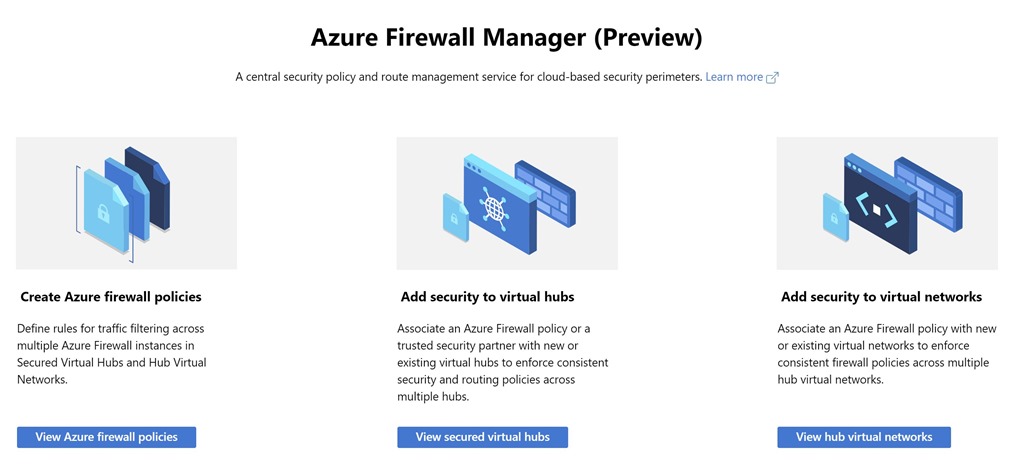
Today, extending Azure Firewall Manager preview to include automatic deployment and central security policy management for Azure Firewall in hub virtual networks.
Azure Firewall Manager preview is a network security management service that provides central security policy and route management for cloud-based security perimeters. It makes it easy for enterprise IT teams to centrally define network and application-level rules for traffic filtering across multiple Azure Firewall instances that spans different Azure regions and subscriptions in hub-and-spoke architectures for traffic governance and protection. In addition, it empowers DevOps for better agility with derived local firewall security policies that are implemented across organizations.
For more information see Azure Firewall Manager documentation.
Hub virtual networks and secured virtual hubs
Azure Firewall Manager can provide security management for two network architecture types:
- Secured virtual hub—An Azure Virtual WAN Hub is a Microsoft-managed resource that lets you easily create hub-and-spoke architectures. When security and routing policies are associated with such a hub, it is referred to as a secured virtual hub.
- Hub virtual network—This is a standard Azure Virtual Network that you create and manage yourself. When security policies are associated with such a hub, it is referred to as a hub virtual network. At this time, only Azure Firewall Policy is supported. You can peer spoke virtual networks that contain your workload servers and services. It is also possible to manage firewalls in standalone virtual networks that are not peered to any spoke.
Whether to use a hub virtual network or a secured virtual depends on your scenario:
- Hub virtual network—Hub virtual networks are probably the right choice if your network architecture is based on virtual networks only, requires multiple hubs per regions, or doesn’t use hub-and-spoke at all.
- Secured virtual hubs—Secured virtual hubs might address your needs better if you need to manage routing and security policies across many globally distributed secured hubs. Secure virtual hubs have high scale VPN connectivity, SDWAN support, and third-party Security as Service integration. You can use Azure to secure your Internet edge for both on-premises and cloud resources.
The following comparison table in Figure 2 can assist in making an informed decision:
| Hub virtual network | Secured virtual hub | |
| Underlying resource | Virtual network | Virtual WAN hub |
| Hub-and-Spoke | Using virtual network peering | Automated using hub virtual network connection |
| On-prem connectivity | VPN Gateway up to 10 Gbps and 30 S2S connections; ExpressRoute | More scalable VPN Gateway up to 20 Gbps and 1000 S2S connections; ExpressRoute |
| Automated branch connectivity using SDWAN | Not supported | Supported |
| Hubs per region | Multiple virtual networks per region | Single virtual hub per region. Multiple hubs possible with multiple Virtual WANs |
| Azure Firewall – multiple public IP addresses | Customer provided | Auto-generated (to be available by general availability) |
| Azure Firewall Availability Zones | Supported | Not available in preview. To be available availabilityavailablity |
| Advanced internet security with 3rd party Security as a service partners | Customer established and managed VPN connectivity to partner service of choice | Automated via Trusted Security Partner flow and partner management experience |
| Centralized route management to attract traffic to the hub | Customer managed UDR; Roadmap: UDR default route automation for spokes | Supported using BGP |
| Web Application Firewall on Application Gateway | Supported in virtual network | Roadmap: can be used in spoke |
| Network Virtual Appliance | Supported in virtual network | Roadmap: can be used in spoke |
Figure two – Hub virtual network vs. secured virtual hub
Firewall policy
Firewall policy is an Azure resource that contains network address translation (NAT), network, and application rule collections as well as threat intelligence settings. It’s a global resource that can be used across multiple Azure Firewall instances in secured virtual hubs and hub virtual networks. New policies can be created from scratch or inherited from existing policies. Inheritance allows DevOps to create local firewall policies on top of organization mandated base policy. Policies work across regions and subscriptions.
Azure Firewall Manager orchestrates Firewall policy creation and association. However, a policy can also be created and managed via REST API, templates, Azure PowerShell, and CLI.
Once a policy is created, it can be associated with a firewall in a Virtual WAN Hub (aka secured virtual hub) or a firewall in a virtual network (aka hub virtual network).
Firewall Policies are billed based on firewall associations. A policy with zero or one firewall association is free of charge. A policy with multiple firewall associations is billed at a fixed rate.
For more information, see Azure Firewall Manager pricing.
The following table compares the new firewall policies with the existing firewall rules:
| Policy | Rules | |
| Contains | NAT, Network, Application rules, and Threat Intelligence settings | NAT, Network, and Application rules |
| Protects | Virtual hubs and virtual networks | Virtual networks only |
| Portal experience | Central management using Firewall Manager | Standalone firewall experience |
| Multiple firewall support | Firewall Policy is a separate resource that can be used across firewalls | Manually export and import rules or using 3rd party management solutions |
| Pricing | Billed based on firewall association. See Pricing | Free |
| Supported deployment mechanisms | Portal, REST API, templates, PowerShell, and CLI | Portal, REST API, templates, PowerShell, and CLI |
| Release Status | Preview | General Availability |
Figure three – Firewall Policy vs. Firewall Rules
